Best Practices in Cyber Incident Prevention for SMEs
Reading Time: 4 Minutes
As a small business owner, you may think you are “too small” to be the target of cybercrime because you aren’t a giant, multimillion-dollar company. However, this couldn’t be further from the truth. Although the media mainly focuses on attacks on big businesses, small businesses are low-hanging fruit for cybercriminals.
Recommended Read: Cybersecurity – what should every business owner know?
Cybercriminals know that small businesses are less likely to have strong security measures in place, making it easier for them to breach their data. In this blog post, you’ll learn the steps you can take to protect your business from the claws of cybercriminals.
Follow These Cyber Incident Prevention Best Practices
While there is no single silver bullet for preventing all incidents, some best practices can help you reduce the risk of falling victim to a cyberattack.
Ensure your cybersecurity policy supports remote work
When implementing a cybersecurity policy supporting remote work, consider the following:
- How will employees access company resources off-site?
- What security measures should be put in place to protect company data?
- How will remote employees collaborate and share data?
Additionally, you should identify any support mechanisms to help employees struggling to adjust to remote work. By taking these factors into account, you can create a cybersecurity policy that is productive, seamless and secure.
We have a number of articles that can help you structure your remote working policy and support your team, such as:
How to ensure compliance when working remotely?
Securing your hybrid work environment
Securing company data with a remote workforce
Provide cybersecurity awareness training for employees
Implementing a security awareness training program for employees is critical in today’s digital age. As a responsible business executive, you must strive to ensure that the program is comprehensive, engaging and adaptable to new threats.
Read: Why security awareness training is essential
Deploy software patches
Threats to your network security are becoming more prevalent as technology advances. That’s why it’s critical to keep your software up to date with the latest security patches.
There are two different ways to keep your software up to date. One way is to set your software to update automatically, while the other is to manually check for updates regularly.
Have active antivirus and anti-malware protection
There are numerous antivirus and anti-malware solutions in the market, so select one that is appropriate for your company. When doing so, you’ll have to consider the size of your company, the type of data you need to safeguard and your budget.
Learn more about Antivirus and Malware
We recommend a cloud-based solution that won’t demand too much from your machines and will always remain up to date. There’s still a strong perception that having an anti-malware solution is enough to protect your business, but that’s not the case! Multiple solutions are required to create layers of protection and avoid threats.
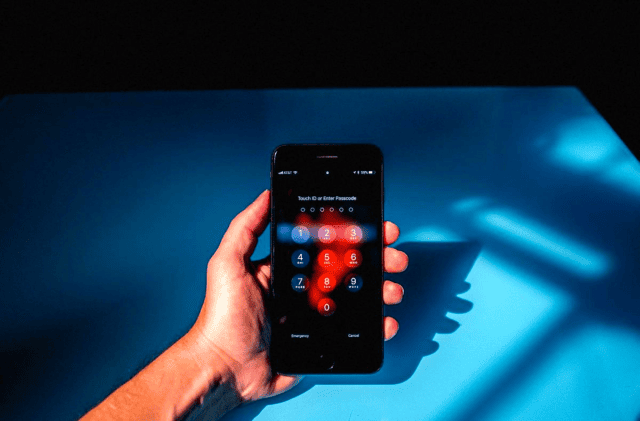
Implement multifactor authentication (MFA)
Multifactor authentication is a security measure that requires users to provide more than one form of identification when accessing data, thus reducing the chances of unauthorized data access. This can include something that the user knows (like a password), something that the user has (like a security token) or something that the user is (like a fingerprint).
Read: Why should every Irish Business implement MFA?
Today, most businesses and applications can benefit from the extra security layer MFA provides. It makes your accounts much harder to hack if your credentials are leaked in a data breach and complement a strong password policy.
Use a virtual private network (VPN)
A virtual private network encrypts your company’s data and allows you to control who has access to it. This can help prevent data breaches and keep your company’s information safe. However, make sure to choose a reputable provider that offers robust security features.

Deploy single-sign-on (SSO) and password management
A single sign-on solution can make your users’ login process easier by allowing them to log in once to a central system and access all the other applications and systems they require. This can make the login process safer and more efficient for them.
In addition to SSO, a password management solution simplifies the user login process by allowing them to manage their passwords more securely and efficiently. Learn more about good password practices in our blog: Your business needs stronger passwords.
Encrypt your data
Data encryption is the process of converting information into a code that can only be deciphered by someone with the key to decrypt it. It is done to prevent unauthorized individuals from accessing the information.
Learn more: PC and Mac Encryption
Data encryption is a critical tool in cybersecurity since it can help reduce the exposure of your data to risks and ensure compliance with data privacy regulations. It is incredibly useful to avoid data breach incidents if someone in your business loses your corporate device.
Have backup and disaster recovery solutions
It is critical to have backup and disaster recovery solutions in place in case of system failure or data loss. To ensure that your backup and disaster recovery solutions are working correctly, you must test them on a regular basis.
You should always have multiple recovery solutions – and at least one of them must be off-site. A disaster recovery strategy goes way beyond backups, and it’ll allow your company to become resilient. You’ll have a better understanding of your most prominent risks and know how to act in case any of them is triggered.
We have multiple articles and solutions concerning backup and DR, such as:
Monitor, test, restore – making sure that your backups are ready
How backup and disaster recovery protects SMEs
Importance of a secure cloud backup solution for remote workers
Collaborate for success
If you’re a small business owner, you may not have the time or expertise to implement effective cyber incident prevention best practices. However, by partnering with us, you can leverage our experience to build a digital fortress around your business. Contact us today to find out how we can help you protect your business against potential cyber threats.
Thanks for reading! To learn more about Business Technology, read our blogs and follow us on Social Media by clicking below.